My Vendor is Responsible…or Are they?
Passing the Buck
Have you said, “My application provider takes on that responsibility.” Or “I don’t have to do that because I use a third party that deals with the security of the data.” Regardless of whether you are talking about a product or service that you use from a third party; the odds are you are not relieving yourself of the responsibility you think you are. We have all heard the term passing the buck, when it comes to data privacy and security regulators have already mandated that the bucks stop at the data controller, which is you.
We all use third party providers such as software solutions vendors to collect and charge payments. Your customers enter in their credit card or bank account information so you can charge them for your products or services. You feel safe because you are not physically keeping any account information and your software provider says that they only keep a “payment token” which makes the risk of a breach of financial information much lower. However, other personal information that is stored in the system like name, address, phone number, email address, etc. are stored in these systems and if they are breached who is to blame? Yes, they may be PCI compliant, but it doesn’t mean that the breach did not occur, and your reputation or your financial wellbeing will not be impacted.
Although financial information is still a target for criminals, behavioral and personal data is almost as valuable as it helps with targeting higher value targets, especially if they are looking to gain specific information such as credentials.
Data Controller vs Data Processor
The terms data controller and data processor are not commonly used; however, regulators use them to identify and delegate responsibility of the ownership of data. In most cases, a business collecting information on their customer, regardless of where it is stored/input, will be considered the Data Controller and responsible for the privacy and security of the data collected. This does not mean third parties are not responsible for privacy and security, but what they are responsible for does change. Third parties should ensure that their privacy and security standards and practices are equal to or exceed those of the businesses they are contracted with, and businesses are responsible for ensuring the third party continues to abide by these their standards, especially as they change due to reorganization and growth.
Ultimately, the business (the data controller) is responsible for the data they collect, transfer, store, and eventually destroy. Moreover, they are responsible for selecting vendors that will help them attain their goals and responsibility. Third party vendors are not an opportunity to pass the buck, but rather a way to achieve your business goals and your governance requirements.
Limitations of Liability and Indemnification
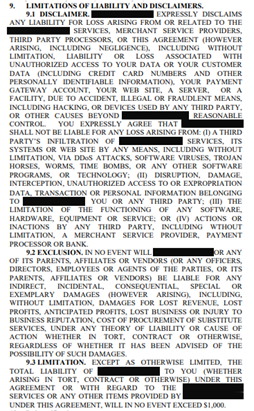
If you have ever reviewed a business contract, you know the words, “limitations of liability” and “indemnification”. It is the first place I go to when I review any business contract. These contract sections outline what is the contractual obligation if there is any loss or “error”, who is responsible and for what. Virtually any contract with any larger organization, like a credit card gateway provider or software provider has the following outlined:
- They have no liability if there is any data loss or access due to unauthorized access
- They have no liability if there is any data loss or access due to fraudulent means
- They have no liability if a third-party infiltration of the systems
How many of these contracts have you signed without reviewing or modifying the limitations of liability and indemnification clauses? Let’s look at this snippet from a service agreement for one of the most widely used payment gateways. Everyone that has signed this agreement has signed away responsibility if there is a loss of data. Contracts are the key to assigning liability and responsibility.
It is natural to only want to accept responsibility for what you feel you have control of. However, business contracts try to legally bind responsibility or lack thereof. Businesses rely on third parties and vendors to provide solutions that help with operational efficiencies such as management of customer data and charging customers. You should not assume your software provider is responsible for the security of the data you are entering into their systems. Each piece of the “system puzzle” wants to limit their liability and ensure they are not responsible for any data loss or financial “injury”. If you walk through the trail of responsibility, it always stops at the beginning, your business.
This year, 5 Privacy Acts are being enforced, California, Virginia, Colorado, Connecticut and Utah and many more are going to be reviewed. You are responsible for the data privacy and security of your employee and customer data, no matter what solutions you are using.
What do you do?
Responsible for privacy and security will always go back to the business. Your customers are unaware of the third-party solutions you contract with, but they do know who you are. Your customers expect to receive products and services without fear of losing their identity.
Third parties will always be a major part of any business. For most businesses, the systems, and applications they use are not “home grown”. Off-the-shelf solutions infuse technology into everyday business. It is critical you take control of your own privacy and security practices.
- Have a privacy and security program in place to manage your risk
- Review vendor contracts (look at the limitations of liability and indemnification clauses)
- Review contracts annually
- Review your access management practices decreasing the likelihood of accidental data access or loss
- Review your privacy policy annually and update your public notice
- Review what data you are sending the vendors and make sure it is not more than what you are contracted to provide
- Change vendors if current vendors are not following your privacy and security practices
Consider additional controls such as cyber-insurance to mitigate your potential financial loss and multi-factor authentication to mitigate loss of credentials and access to data.


